The “Insider Threat” You Overlooked: Proper Employee Offboarding

Protect your business from insider threats with a secure employee offboarding process. Learn how to prevent data breaches, revoke access, and close security gaps effectively.
The 2026 Hybrid Strategy: Why “Cloud-Only” Might Be a Mistake

Why “Cloud-Only” Might Be a Mistake Cloud computing promised speed, simplicity, and scalability. For years, the message was simple: “Move everything to the cloud.” Many businesses did exactly that. However, […]
Managing “Cloud Waste” as You Scale

Cloud waste could be draining your IT budget. Learn how to identify unused cloud resources, implement FinOps strategies, and reduce cloud spending in 2026.
Agentic AI Explained: Risks, Benefits, & 2026 Readiness Guide
Agentic AI is transforming small businesses in 2026. Learn how autonomous AI agents improve efficiency, increase risk exposure, and what security controls you need before deployment.
Windows Server 2016 End of Life
Windows Server 2016 reaches end of support in January 2027. Learn the security risks of unsupported systems and how to plan a safe server upgrade or cloud migration.
Why SMS MFA is no Longer Safe

SMS-based MFA is no longer secure. Learn how SIM swapping, phishing, and interception attacks bypass text codes—and why phishing-resistant MFA, passkeys, and hardware keys are the new standard.
15-Minute Routine to Prevent Misconfiguration and Data Leaks

Protect your business with a simple 15-minute daily cloud security checklist. Prevent data leaks, ransomware, and costly misconfigurations today.
The “Deepfake CEO” Scam: Why Voice Cloning Is the New Business Email Compromise (BEC)

AI voice cloning scams are rising fast. Learn how cybercriminals use deepfake audio to impersonate executives and how to protect your business from vishing attacks.
How Ransomware Attacks Are Shutting Down Cannabis Businesses

Ransomware can shut down a cannabis business in minutes. Learn how attacks happen, why the industry is targeted, and how to prevent costly downtime.
How Hackers Target Cannabis Employees: Phishing Guide
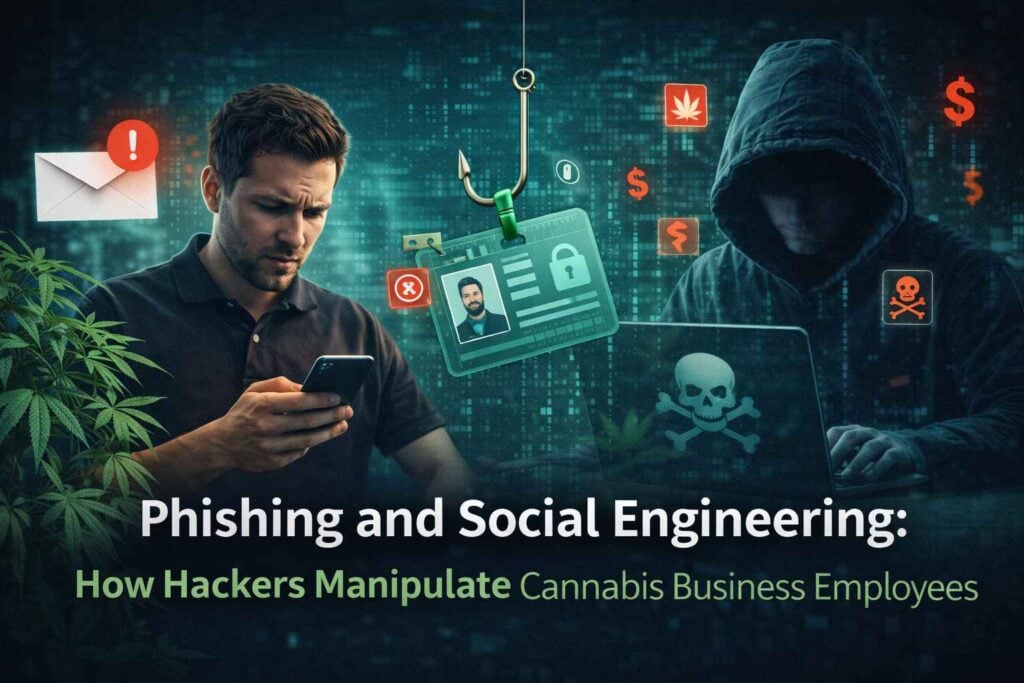
How Hackers Target Cannabis Employees: Phishing Guide It’s 9 AM on a Tuesday morning. Your operations manager opens what looks like an urgent email from your seed-to-sale tracking vendor. “CRITICAL: […]