The 2026 Guide to Uncovering Unsanctioned Cloud Apps
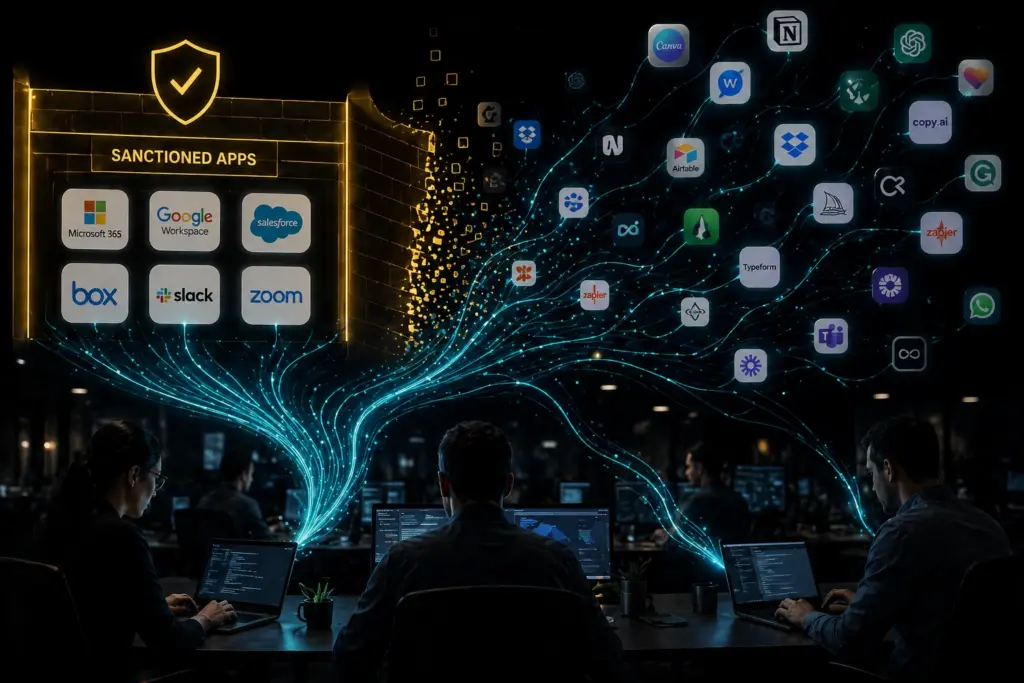
Discover how unsanctioned cloud apps and hidden AI features expose business data and learn a practical workflow to find, assess, and control them
Stop Ransomware in Its Tracks: A 5-Step Proactive Defense Plan

A 5-Step Proactive Defense Plan Stop Ransomware in Its Tracks Why Ransomware Often Starts Small Ransomware is not a sudden event. It builds over time. In many cases, it starts […]
How Shadow AI Becomes A Business Risk

Learn how shadow AI exposes sensitive data and how to audit usage, control risk, and prevent data leaks across unsanctioned AI tools in your business
A Simple Zero Trust Roadmap for Small Business Security

Learn how Zero Trust helps small businesses stop breaches by limiting access, verifying users, and reducing risk from stolen passwords
5 Security Layers Your MSP Is Likely Missing (and How to Add Them)

Top 5 Security Gaps in MSP Environments—and How to Close Them Why Small Business Security Breaks Down Most small businesses do care about security. The issue is not effort. It […]