If you want to find unsanctioned cloud apps, don’t start with a policy. Start with your browser history. :contentReference[oaicite:0]{index=0}
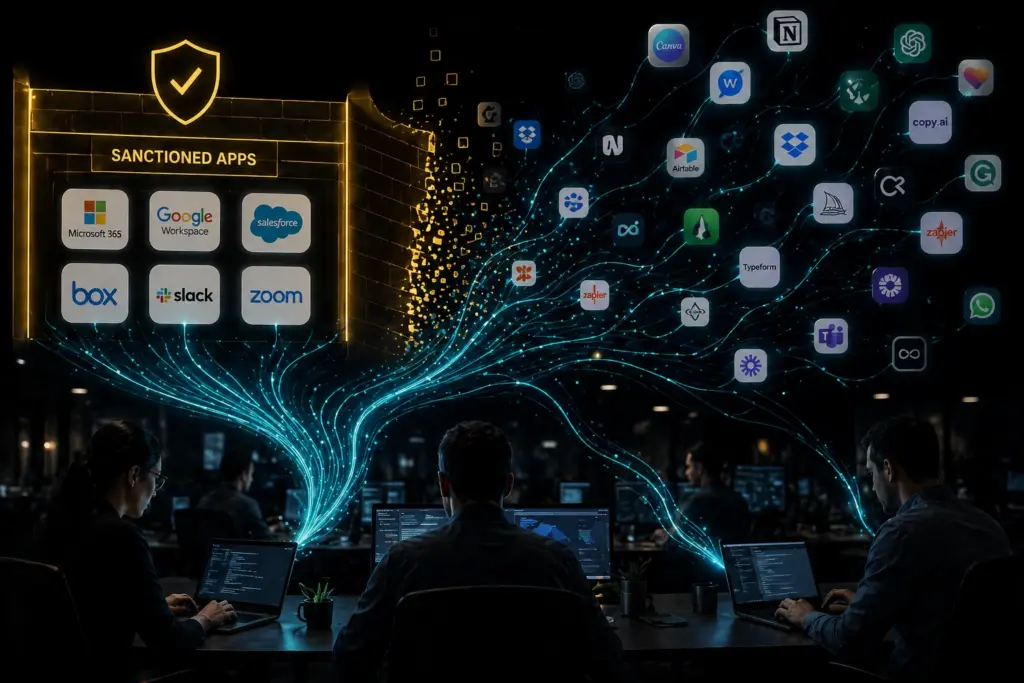
The cloud environment your business really uses rarely matches the official IT diagram.
It grows through small, everyday decisions. A quick file share. A free tool that solves a problem faster. A plug-in added to meet a deadline. An AI feature turned on inside an app you already use.
In the moment, it feels efficient. It feels helpful.
Until it isn’t. Then you realize your data is spread across tools you never approved, accounts you cannot manage, and settings that do not match the actual risk.
Why Unsanctioned Cloud Apps Are a Bigger Risk in 2026
Unsanctioned cloud apps are not new. What has changed is the scale and speed.
Most IT teams think employees use a few dozen apps. In reality, the number is far higher.
Many of those apps have never been reviewed or approved.
This creates a gap between what you think is happening and what is actually happening.
AI Is Expanding the Problem
AI adds another layer.
It is no longer just a separate tool people sign up for. It is built into the apps your team already uses.
This means AI risk can exist without a clear decision to adopt AI.
Employees may also use AI tools on their own to work faster, which increases the chance of data exposure.
Why Blocking Tools Doesn’t Work
Blocking apps used to be the default response.
Today, it often makes things worse.
If you block a tool without offering an alternative, people will find another way to get the job done.
That usually makes the problem harder to see and harder to manage.
Start with Visibility, Not Restrictions
The first step is understanding what is actually happening.
If you treat cloud app use as a discipline problem and respond with bans, you push it out of sight.
A better approach is to measure usage against clear standards.
This helps you focus on risky behavior, not just the tool itself.
Once you have that visibility, you can decide what to allow, restrict, replace, or block.
A Practical Workflow to Manage Cloud App Risk
This is not a one-time clean-up. It is a process you can repeat to stay ahead of new tools and habits.
Step 1: Discover What Is in Use
Start with the signals you already have.
- Endpoint activity
- Identity and login logs
- Network and DNS data
- Browser usage
You cannot manage what you have not identified.
Step 2: Analyze Usage
Do not stop at listing tools.
Look at how they are used.
- Who is accessing each app
- What level of admin activity exists
- How data is shared
- Whether old access still exists
Step 3: Prioritize Risk
Not all apps carry the same risk.
Focus on:
- The sensitivity of the data
- How information is shared
- The strength of identity controls
- The level of visibility you have
- Whether AI features could expose data
Step 4: Tag and Classify Apps
Make decisions clear and repeatable.
Label apps as:
- Approved
- Restricted
- Unsanctioned
This allows you to track progress and apply consistent action.
Step 5: Take Action
Once apps are classified, enforce the decision.
- Warn users about risky behavior
- Restrict usage where needed
- Block high-risk apps with a clear plan
Make changes gradually and communicate clearly to avoid disruption.
Build a Repeatable Process
Unsanctioned cloud apps are not going away. They will continue to grow, especially as AI becomes part of everyday tools.
The goal is not to block everything. It is to create a repeatable model.
Discover what is in use. Decide what is acceptable. Enforce those decisions with clear guidance and safer alternatives.
When you do this consistently, cloud app sprawl becomes manageable instead of unpredictable.
If you need help building a practical approach, a structured process can help you gain visibility, reduce risk, and keep your team productive – schedule a one-on-one with our team to review your approach.