Managing “Cloud Waste” as You Scale

Cloud waste could be draining your IT budget. Learn how to identify unused cloud resources, implement FinOps strategies, and reduce cloud spending in 2026.
Agentic AI Explained: Risks, Benefits, & 2026 Readiness Guide
Agentic AI is transforming small businesses in 2026. Learn how autonomous AI agents improve efficiency, increase risk exposure, and what security controls you need before deployment.
Windows Server 2016 End of Life
Windows Server 2016 reaches end of support in January 2027. Learn the security risks of unsupported systems and how to plan a safe server upgrade or cloud migration.
Why SMS MFA is no Longer Safe

SMS-based MFA is no longer secure. Learn how SIM swapping, phishing, and interception attacks bypass text codes—and why phishing-resistant MFA, passkeys, and hardware keys are the new standard.
How Hackers Target Cannabis Employees: Phishing Guide
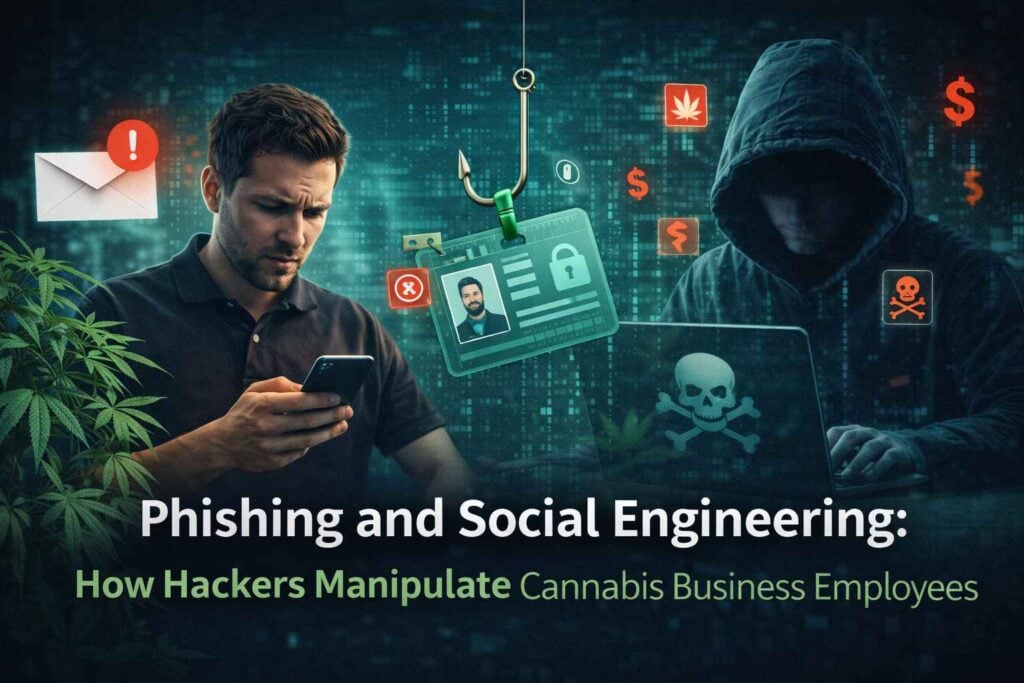
How Hackers Target Cannabis Employees: Phishing Guide It’s 9 AM on a Tuesday morning. Your operations manager opens what looks like an urgent email from your seed-to-sale tracking vendor. “CRITICAL: […]
Manage Contractor Access with Conditional Access: 60-Minute Implementation Guide

Learn how to secure contractor access using Microsoft Entra Conditional Access. Automate access, enforce least privilege, and revoke logins automatically.
Secure Guest Wi-Fi with a Zero Trust Approach

How to Secure Guest Wi-Fi with a Zero Trust Approach Guest Wi-Fi is a convenience your visitors expect and a hallmark of good customer service. But it’s also one of […]
Follow these Steps for ZERO Risk Holiday Shopping This Year

Follow These Steps for Zero Risk Holiday Shopping This Year Holiday shopping has never been easier. With one click, you can order gifts, supplies, and everything in between. But this […]
Beware the “Tap-to-Pay” Trick: How Ghost Tapping Puts Shoppers at Risk

Tap-topay has become a part of everyday life. You tap your phone or card, hear the beep, and you’re on your way.
No swipe, no PIN, no signature. For busy shoppers and small businesses alike, it feels like the perfect mix of speed and convenience.
But that same convenience is now being twisted into a new kind of scam called “ghost tapping”—
and it’s hitting shoppers who think they’re making a normal purchase.
How to Use AI for Business Productivity While Staying Cyber-Secure
AI can supercharge productivity—but only with guardrails. Learn how SMBs can adopt AI securely with clear policies, enterprise-grade tools, access controls, and continuous monitoring. Turn AI into a security asset, not a liability.