Looking for a tech-savvy Junior Assistant!

Caldera Cybersecurity Services is seeking a motivated and reliable Junior Assistant to help keep our online presence strong and our operations running smoothly. This is a new role at a growing, community-focused […]
Want to Know YOUR Security Maturity?

🚀 Introducing Our Free Security Assessment Tool – Based on the CMMC Model! We’re excited to announce the launch of our free Security Assessment Tool, now available at 👉 https://assessment.calderacyber.com! […]
BBB Essential Security Summit
From cyber threats to physical risks, the BBB Business Shield Summit arms you with the tools, insights, and connections to keep your organization safe. Join business leaders, security professionals, and […]
SAFEGUARD YOUR BUSINESS WEBINAR

When: Wednesday, October 15, 2025 | 11AM to 12PM Mountain | Online Presentation Caldera Cybersecurity Services is hosting a free webinar to help small business owners understand and fight back […]
7 Unexpected Ways Hackers Can Access Your Accounts

7 Sneaky Ways Hackers Break In—and How Small Businesses Can Fortify Their Defenses Technology has made our lives a breeze—but it’s also made life easier for the bad actors lurking […]
Zero Day Café Episode #2
Email bombing isn’t just inbox chaos—it’s a serious and evolving threat. In this episode, we break down the mechanics behind email bombing, its use as a smokescreen for deeper threats, and the most practical defenses for small businesses and beyond.
Drowning in the Inbox: How Mailbombing Disrupts Business — and How to Fight Back
Mailbombing is a type of cyberattack designed to swamp a target’s inbox with a massive surge of emails in a short time. The emails themselves aren’t usually malicious—no viruses, no phishing links—just sheer volume.
Phish-Proof Founders Cybersecurity Event
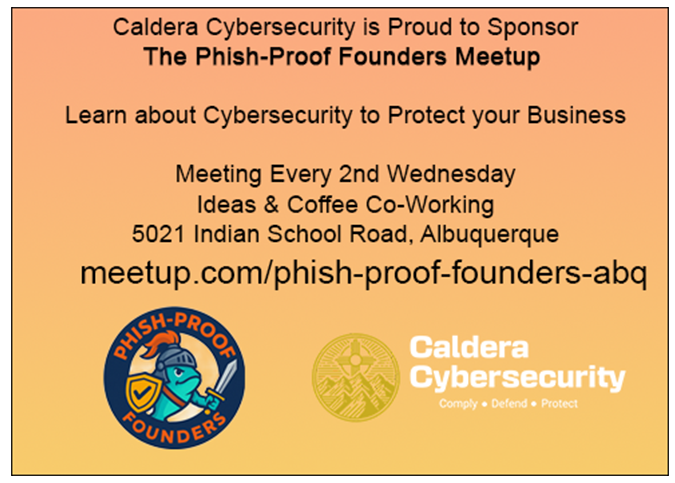
Phish-Proof Founders is holding their monthly meeting on Wednesday, August 13, 2025 from 6pm to 7:30pm at the Ideas and Coffee Coworking Space in Albuquerque, NM. All are invited. Please […]
How to Protect Your Business Data Before Disaster Strikes

Protect your business from data loss with simple backup and recovery strategies. Learn how to reduce downtime, stop cyber risks, and recover fast.
Want to know if you have been hacked?

Free Compromise Check: Is Your Email in the Wrong Hands? Ever wondered if your email has been floating around in the dark corners of the internet? Now you don’t have […]